You also know that even the most comprehensive and layered security stacks miss most threats. According to Ponemon’s Cost of a Data Breach Report 2020, it takes about 280 days to identify and contain a data breach. That’s 40 weeks or over 9 months to control the situation.
Instead of months of unknown detection, imagine if you could spot the real threats within minutes.
By leveraging and automating the best security tools, you can. But how do you take millions of alerts and identify which ones are real, which ones are high risk, and which ones correlate across different tools? The answer is behavioral analytics.
What is Behavioral Analytics & How Does it Apply to Cybersecurity?
The average enterprise has 75 different cybersecurity tools, yet somehow threats are still getting by. How?
Chasing an elusive magical answer in the latest security tools can help you make incremental improvements to your security posture, but they aren’t enough.
More organizations than ever find the solution is to apply analytics to all of the cyber data you already have with user behavior analytics.
Behavioral and entity analytics, also referred to as just user behavior analytics (UBA), studies consumer behaviors, habits, and patterns to model and predict their activities and choices.
In applying behavioral analytics to cybersecurity, we create predictive modeling to identify threats missed by existing cyber tools or manual effort.
How Behavioral Analytics Differs from Your SIEM System
You may be thinking, “I have analytics” in place today through various SIEM, SOAR, NTA, UEBA, and other products.
But while leading Security and Information Event Management (SIEM) products focus on collecting and analyzing logs to spot correlation through predefined rules, they don’t take the analysis as far as behavioral analytics tools.
The four key differences between other analysis and user behavioral analytics are that:
1. It analyzes and correlates threats across products and data sources
Behavioral analytics pulls data from various software tools to identify anomalous activity across your network. Similar to how firewalls and antivirus software analyze data to detect new, zero-day threats, behavioral analytics cross-references this data to correlate seemingly innocuous events and identify threats. User behavioral analytics identifies signals showing user actions that break from patterns, like location or naming conventions, and looks at activity, apps, and accessed files. It identifies anomalous activity whether it comes from an external hacker, an insider, or malicious software.
2. It analyzes and correlates threats across large spans of time
Leading SIEM and Log Management tools rely on a query-based, batch processing approach to retrieving data. Batch processing has two critical deficiencies; it requires large amounts of data to remain online and queryable and often requires restoration of backups before viewing data archived for storage costs. Maintaining online data and restoring backups is budget and time-consuming and is frequently skipped during threat analysis.
Cybraics developed a new method of storing unique behaviors in a relational database called Persistent Behavior Tracing. It intelligently tracks behaviors found in multiple log entries over an unlimited timeframe and deduplicates this data, allowing for historical contextual view, and extracting relevant attributes required for the analyst to make sense of the event, even if the original logs are archived.
3. It automates the analysis and eliminates manual effort to prioritize threats
One of the repeated themes across cyber threat analysis is that human effort is the limiting factor. If a SIEM product can reduce 100,000,000 alerts down to 100,000, you still need an army of analysts to identify which ones are legitimate threats. Identification and correlation between log sources are critical to the accurate prioritization of threats. False positives litter typical SIEM and SOAR tools, doing little to resolve alert fatigue.
Behavioral analytics, when powered by automation, alleviate the bulk of the effort. When powered by machine learning and A.I., they deliver a force-multiplier that reduces 100,000,000 alerts down to a few hundred actionable cases.
4. It applies machine learning and A.I. to the analytics
Not all claims of A.I. are the same. Rule and signature-based analysis engines are severely limited in adapting to and recognizing new threats because they run on pre-written sets of instructions. They run on batch processing and require baselining and continual tuning.
Today’s threats require a dynamic machine learning and A.I.-based behavioral analytics engine that responds to the ever-changing sophistication and tactics used. Real-time streaming analysis is also critical to finding threats as they appear to help you respond to incidents.
Ready to Apply User Behavioral Analytics?
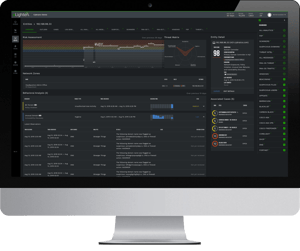
With over 250 machine learning and A.I.-based behavioral analytic detections, Cybraics helps you identify and respond to threats more efficiently and accurately. To learn more about user behavioral analytics and see it in action, schedule your free demo today.
