Do you rely on security information and event management (SIEM) tools for real-time analysis of security alerts? If so, then you know a SIEM helps store, organize and support the analysis of log data and alerts.
But many don’t realize their SIEM is only scraping the surface of information and event management since the tool still requires time-consuming manual correlation.
That’s where an autonomous SIEM becomes vital for the efficiency and accuracy of your true threat landscape. First, let’s look at what makes a SIEM autonomous and how it differs from other SIM, SEM, or SIEM tools.
What Exactly Is an “Autonomous” SIEM?
Your security information and event management may compile alerts, but can it intelligently categorize them and correlate them? Is your current SIEM signature or rule-based, meaning it runs what you told it to recognize? Odds are, your existing SIEM isn’t as automated as you need, and manual effort dominates your time and effort to identify threats.
If you want a SIEM that learns and continually evolves its threat detection and prioritization based on your unique cybersecurity environment, you need a better SIEM.
A truly autonomous SIEM is the solution.
Here’s how an autonomous SIEM outmatches traditional SIEMs and related tools:
An Autonomous SIEM Reduces Manual Effort.
Typical log management tools produce hundreds of millions of alerts each month. SIEM tools help reduce this to hundreds of thousands— but that still leaves hundreds of thousands of potential threats to review. Moreover, with headcount in the cybersecurity field at an all-time shortage and those with qualified skills in such high demand, it’s unrealistic to expect to address all those alerts manually.
An autonomous SIEM cuts down the alert noise by automating the process. This automation simplifies organization and prioritization, empowering your IT team with the transparency needed to investigate and mitigate cyber threats at scale. Specifically, it scales down the demand on your team instead of leaving you to scale up your team. 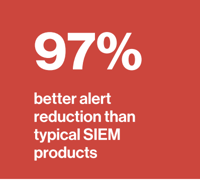
Here at Cybraics, our autonomous SIEM reduces alerts by an incredible 97% compared to even the best SIEM plus automation tools combined. As a result, you can put an end to alert fatigue — once and for all.
An Autonomous SIEM Automates Case Creation.
A traditional SIEM may flag thousands of alerts, but without correlation and prioritization, human effort is required to analyze and distill these down to urgent threats.
An autonomous SIEM uses rules and signatures to handle the basics, and more importantly, it leverages artificial intelligence (AI) and machine learning (ML) based behavioral analytics to adapt to unknown and new threats. Then, an autonomous SIEM takes it a step further by automating case creation for these alerts in a way that other standard SIEM tools cannot.
Instead of thousands of alerts, you see actionable cases. With an autonomous SIEM like Cybraics, you even receive guided remediation and case orchestration to resolve prioritized threats quickly. Our autonomous SIEM offers a 96% automated case creation rate, and our expert security operations center (SOC) team covers the rest.
An Autonomous SIEM Breaks Through Silos in Your Existing Tech Stack.
Because IT teams are so inundated with alerts across dozens of different threat detection tools, 31% of security alerts go uninvestigated due to sheer volume and alert fatigue.
The right SIEM can eliminate redundant tools and bridge the gaps between your existing tools.
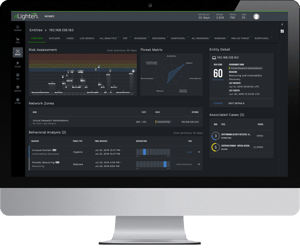
Cybraics’ nLighten Autonomous SIEM enhances over 80 leading security products like Palo Alto, CrowdStrike, Carbon Black, SentinelOne, and more — while automatically detecting threats otherwise missed by security tools.
An Autonomous SIEM Reduces Your Cyber-related Costs.
There are quite a few ways an autonomous SIEM can improve your cybersecurity ROI. An automated threat detection and case creation solution simplifies your operations by replacing existing tools and cutting down on technical expenses. Persistent Behavior Tracing also reduces storage needs and costs while retaining the historical context and cross-product log/alert correlation needed for proper identification.
Let’s not underestimate the cost of a breach. One 2020 study by Ponemon Institute found that those with automated security protocols vs. those without reduced the financial impact of a breach by 59 percent. An autonomous SIEM gives you the true transparency of the threat landscape you need to reduce your cybersecurity risks.
The World's Only Autonomous SIEM and MDR Solution
Ready for a truly autonomous SIEM? Born from a DoD program designed to advance cybersecurity through ML and AI, Cybraics offers the most advanced automated SIEM and managed detection and response (MDR) solution: nLighten.
To learn more about our autonomous SIEM, view our comprehensive datasheet.
Want to see if your cybersecurity is up to par? Download your free eBook: The 4 Warning Signs Your Cybersecurity Needs an Overhaul & How to Fix It.